|
The
Henna Page Tech Pages
Shields up! Part 2 The Firewall is your Friend! by Roy Jones © 2004 - 2007 Any computer that connects to the Internet is a potential target for malware and hackers. This is especially true if you have a broadband connection, but dialup users are at risk as well. Part of the problem is the nature of the Internet itself. The technical standards that determine the design of the Internets systems and the networking software and hardware on your computer were designed for ease of communication rather than security. The Internets protocols were designed in a more innocent time, when the user community was made up almost entirely of academics, engineers and technicians who were involved in building the system and had nothing to fear from each other. Today, however, the Internet is open to one and all and not everyones motives for using the network are as pure as wed like. Your ISP may have some built-in
security systems for its users, but you also need to take care of
yourself.
Remember the online safety mantra:
The responsibility for my
computers security is mine and mine alone.
Part of any good personal computing security regimen is to install a firewall. A firewall is a device that monitors incoming and outgoing data and allows only the data permitted by a predetermined rule-set to pass. One of the most basic firewall rules is one I call the speak only when spoken to rule. This basic rule allows a remote Internet host to connect to your computer only if your computer initiated the connection. This helps to keep another computer from making a stealthy connection to your PC and uploading or downloading data without your knowledge. Another basic firewall rule is to ignore all PING requests. PING is a networking utility that sends a short data stream to a computer and asks it to answer by sending back a data stream of its own. Network administrators use PING and its more advanced cousin TRACERT, to test for connectivity and to see if a remote computer is live on the network. A firewall can be configured to drop all PING and TRACERT packets and not return an answer, so as far as the requesting computer is concerned, the computer behind the firewall doesnt exist. These two firewall rules can go a long way toward keeping malicious network users and programs from finding a way into your computer. I mentioned earlier that a
firewall also keeps track of data leaving the computer. This is
important if you need to keep the PC from being used for certain things
such as online gaming. The firewall can be configured to recognize
packets bound for a specific destination and drop them so the computer
cant open communication with the remote site.
The firewall also maintains an activity log showing contact attempts by remote computers and any outgoing data that it has blocked. Much of the activity from the Internet side of your firewall will be legitimate scans run by the administrators at your ISP, or curious network users pinging to see whats out there. Some of the activity, however, wont be so innocent, and keeping the possibly malicious probes from entering your system or home network is why you should always have a firewall installed and in good order. Firewalls are available both as hardware and software. One of the best known software firewalls is ZoneAlarm. ZoneAlarm comes in several versions, including a basic, freeware version that you can download from their site at http://www.zonelabs.com. The free version of ZoneAlarm comes with enough features and flexibility to provides basic protection against intruders. The commercial versions of ZoneAlarm come with more advanced features, including an annual subscription to ZoneLabs update services. Software firewalls can usually be configured to alert the user through a visible or audible alarm, as well as logging a security incident with the IP address of the remote host, the date, time and the port on your PC that the remote host tried to enter. A number of other manufacturers,
including some of the better known anti-virus companies, include
software firewalls in their product lines, either as standalone
products or as part of a security suite. FirewallGuide.com, http://www.firewallguide.com/software.htm,
is a good place to look for product reviews and links to manufacturers.
A software firewall is the only convenient option for dialup users, but if you have a broadband connection to the Internet (DSL, or cable), you should have a hardware firewall between your PC (or your household network) and the output from your ISP. A typical residential hardware firewall is usually part of a device popularly known as a broadband router. The router is a multifunction device that can provide several valuable services to a home network.
The router/firewall will have a Web interface for accessing its administrative controls. The screenshot below shows one of the admin pages for my own router, including the textboxes for setting and changing the administrators password and buttons to display the log, upgrade the routers firmware and reboot the router. 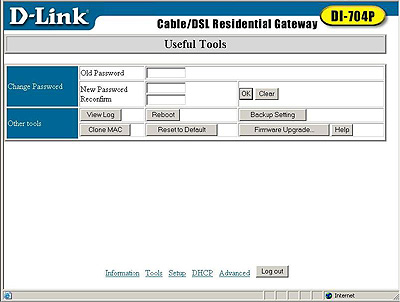 An advantage of a hardware firewall for broadband users is that the firewall, like the broadband connection itself, is always on, so the firewall is already up and running any time you turn on your PC. Also, hardware firewalls are less likely than software firewalls to be compromised by viruses and other malware, and because it is fully independent of the computer, a hardware firewalls operation is not affected if some software or operating system defect causes a malfunction in the computer. Having said that, let me remind
you that Im a firm believer in defense in depth. I have a hardware
firewall between my cable modem and my home network, but I also have
software firewalls installed on every computer in the house. This means
an intruder would have to clear two hurdles to get to any host on our
mini-LAN, that there is some level of protection running, even if one
of the devices should fail, and that when we use dialup, for example as
a fallback if the cable fails, there is still a firewall running on any
host connected to the Internet.
FirewallGuide.com, http://www.firewallguide.com/hardware.htm, has information and product reviews on several router/firewall combos for both wired and wireless home and small office use. What Ive laid out here barely scratches the surface of firewalls, but it should be enough to persuade you that you need one as part of your personal computer security regime and to help you make some intelligent decisions about what to buy. I havent gone into any of the details of configuration, but they vary from one product to another, and information is available in the manuals or on the manufacturers web site. You can e-mail specific computer questions to Roy Jones at streetleveltech@hotmail.com. Back to The Henna Page Tech Pages
Index Can't find what you want
here?
Try The Henna
Page
Main Index. |